Encryption | The key to compliance and trust

Explore the powerful connection between encryption and achieving regulatory compliance, ensuring data security and customer trust.
Published by

Simone Catania
Date
In today’s digital landscape, it’s crucial to understand the role encryption plays in safeguarding sensitive data. Encryption effectively prevents unauthorized access to data and communications by converting information into a code that can only be deciphered with a decryption key. Organizations that use encryption can significantly boost their data security, minimize the risk of data breaches and align their strategies with regulatory standards. Governments worldwide have long acknowledged the importance of establishing regulations to protect private user information on the internet and have enacted laws with stringent protection requirements. Legislators have mandated or suggested encryption as the best practice organizations should apply when sharing or storing sensitive information.
We’ll explore how encryption and compliance are connected and examine important laws that support encryption. Furthermore, we’ll show you how your business can not only adhere to national regulations but also foster solid customer relations built on trust!
Protecting data amidst the surge in cybercrime
Taking measures to secure sensitive data and communications and earn customer trust has become more important than ever. Organizations around the globe are faced with the challenge of safeguarding sensitive information. Approximately 3.5 quintillion bytes of data is generated daily and this staggering volume of data must be protected against cybercrime, which itself is developing and growing at an alarming rate. It is estimated that the damage caused by cybercrime will hit $8 trillion in 2023 and rise to $10.5 trillion by 2025. Every single second, 68 records are lost or stolen. The global average cost of a data breach in 2023 will amount to $ 4.35M. In this scenario, the implementation of robust and reliable security protocols like encryption to ensure the safety and protection of sensitive data and information is not only common sense, but absolutely crucial.
Hard-hitting cybercrime numbers for 2023
- 68 records lost or stolen every second
- $8 trillion the cost of cybercrime, rising to $10.5 trillion by 2025
- $4.35M global average cost of data breaches
Encryption powers data security
The extensive history of encryption stretches over millennia and is intertwined with cryptography studies. It has played a crucial role in safeguarding trade secrets, military correspondence, confidential personal data and, recently, information saved on devices.
The concept behind encryption is simple: It protects sensitive information by converting it from a readable format (plaintext) into an unreadable format (ciphertext). Only authorized users with the appropriate encryption key can access and decipher the encrypted content. While encryption alone doesn’t prevent content interception on the internet, it plays a central role in a comprehensive information protection strategy.
Several encryption techniques and protocols, like TLS/SSL, S/MIME, and code signing, aim to protect data during transmission and storage and ensure authenticity and integrity, whether for executables, emails, chat messages or general online communication and data transfer. Moreover, it’s possible to implement multiple layers of encryption simultaneously. For instance, you can implement S/MIME to encrypt emails and add another layer of protection by securing the communication channels through which they travel with TLS/SSL, ensuring that only authorized recipients can access the information.
By employing encryption, you can be confident that your data remains inaccessible to unauthorized parties, even if it is intercepted.
Encryption for data at rest vs. data in transit
Encryption is vital for the protection of two fundamental data types: data at rest and data in transit. By understanding the distinctions between these data types, you can establish a rock-solid data security strategy that keeps your valuable information out of the wrong hands.
Data at rest refers to information stored on devices like hard drives, servers or backup systems. Encryption for data at rest aims to shield this stored data from unauthorized access, tampering or theft. By encrypting data at rest, you can make sure that, even if an attacker gains access to your storage devices, they can’t read or use the information without the proper decryption key. Data-at-rest encryption examples include full-disk encryption, file-level encryption and database encryption. On the other hand, data in transit refers to information actively moving between locations, such as over the internet, network connections or between devices. Encryption for data in transit aims to safeguard the data during transmission, ensuring that unauthorized parties can’t intercept, read or modify it. Data in transit encryption examples include TLS/SSL for securing web connections, HTTPS for safe browsing and encrypted messaging protocols for secure communication.
Encrypting both data types is essential for a comprehensive data security plan, as it helps protect sensitive information from unauthorized access, whether stored or in transit.
Safety goes beyond firewalls and passwords
Can you protect data and communications with firewalls and passwords? Although these are important components of data security, they are often insufficient to prevent data breaches and cannot offer proper all-around protection.
This is easily explained. Firewalls and passwords typically focus on creating a barrier against unauthorized access but do not actually protect the data. For instance, firewalls act as a shield between a trusted network and untrusted external networks, but sophisticated hackers can bypass them or they can even fail due to misconfiguration. Similarly, passwords can easily be cracked or stolen through phishing attacks, social engineering or brute force techniques. This is where encryption steps in to protect information. By encrypting data, it is transformed into a format that is unreadable without the correct decryption key. Even if a breach occurs and unauthorized individuals gain access by breaking firewalls and passwords, the encrypted data remains secure and useless to them without the decryption key. In this manner, encryption adds an extra layer of protection to sensitive information, ensuring its safety even in a data breach.
Encryption methods Encrypting data at rest Use full-disk encryption (e.g., BitLocker for Windows, FileVault for macOS), file-level or database encryption. Securing web connections Implement TLS/SSL protocols to establish a secure connection between a web server and a client (browser). Encrypting emails Employ end-to-end encryption tools like PGP or S/MIME to secure email content and attachments. Encrypting files before sharing Utilize tools like 7-Zip, VeraCrypt or AxCrypt to encrypt files or create encrypted containers for sharing. Protecting data in transit Apply encryption protocols like TLS/SSL, HTTPS or encrypted messaging platforms (e.g., Signal, WhatsApp). Verifying the authenticity of software Implement code signing to sign software, ensuring its integrity and authenticity. Protecting DNS communications Use DNSSEC and DNSCrypt to protect domain names from spoofing and ensure the authenticity of DNS data. Encryption solution for domains Select between domain validation (DV), organization validation (OV), or extended validation (EV) for certificates based on your domain security needs and desired level of trust.
The objectives of encryption with regard to data security
Encryption is crucial in ensuring compliance and data security by safeguarding data from unauthorized access. Various positive aspects highlight its significance in maintaining privacy, adhering to regulatory requirements and fostering customer trust.
1# Data protection
Data protection is a primary concern for businesses and internet users. Encryption helps protect sensitive data from unauthorized access, ensuring the confidentiality and integrity of the information. Encryption effectively shields data from prying eyes and potential breaches by converting data into an unreadable format.
2# Communication security
Communication security is another major aspect of encryption. Encrypted communication channels prevent eavesdropping and interception, securing the exchange of information between parties. This is particularly important for businesses that rely on secure communication for their daily operations, such as financial institutions and healthcare providers.
3# Regulatory compliance
Regulatory compliance is an essential consideration for many industries. Specific regulations require organizations to implement encryption in order to protect sensitive data. Adhering to these regulations ensures compliance and demonstrates a commitment to data security.
4# Reputation management
Robust encryption practices help maintain the trust of clients and customers, contributing to effective reputation management. Implementing strong encryption measures can prevent potential reputational damage resulting from data breaches, which can have long-lasting consequences.
Encryption in laws and regulations
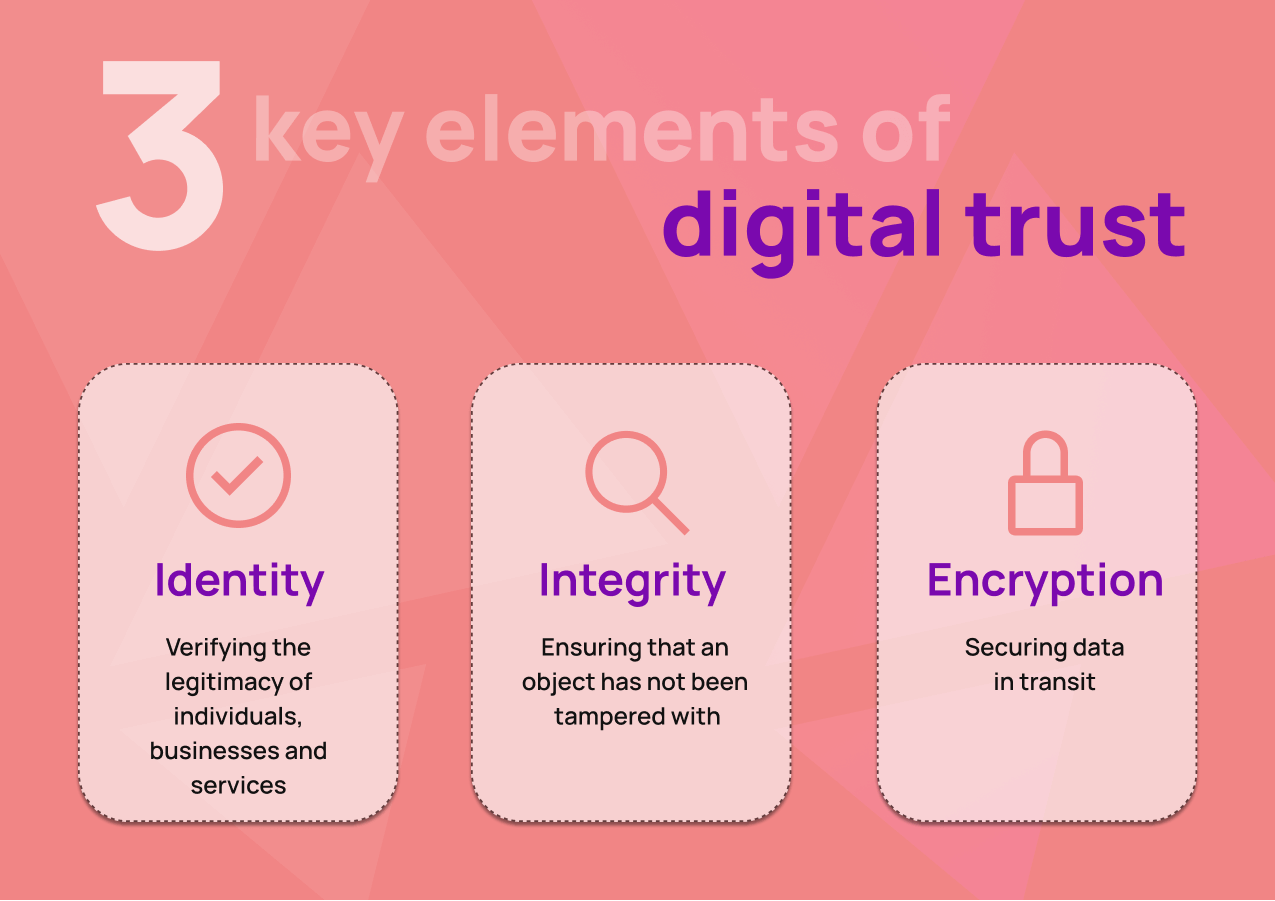
Given the importance of protecting user data online, governments have enacted laws with stringent security measures that companies must implement. These laws and regulations do not endorse specific encryption technologies, products or services. Instead, they focus on mandating that all entities involved in handling data protect the storage and transmission of data through various means. There are three aspects that these regulations seek to protect.
- Retention and disposal policies: Companies must have procedures for the secure retention and disposal of data. This ensures that sensitive information is not kept longer than necessary and is destroyed in a secure manner when no longer needed.
- Processes and procedures: Organizations must implement processes and procedures to protect data confidentiality, integrity and availability. This includes access controls, authentication and regular security audits.
- Rendering information unreadable: Encryption laws and regulations often require companies to render specific types of information (such as personally identifiable information or financial data) unreadable. This can be achieved through encryption or other methods, such as tokenization or data masking.
Encryption laws and regulations aim to protect sensitive data by requiring organizations to implement various policies, procedures,and methods to secure the storage and transmission of data. The focus is not on endorsing specific encryption technologies or products but rather on ensuring that data is protected in a comprehensive and effective manner.
Encryption and compliance: the data protection landscape
Several countries worldwide have implemented laws that directly or indirectly mandate encryption. From the American HIPAA in healthcare to GDPR in the EU and CCPA in California, encryption of protected data classes is required by regulations. Here is an overview of critical laws and their associations with encryption. It offers valuable insights into the complex data protection landscape and the importance of adhering to regulatory standards to mitigate the risk of data breaches and the associated financial and reputational consequences.
1 GDPR
The GDPR (General Data Protection Regulation) is the comprehensive data protection regulation that applies to all organizations operating within and outside the European Union (EU) that process the personal data of EU citizens. Although the GDPR does not explicitly mandate encryption, ensuring data protection and compliance is strongly recommended. Thus, robust encryption measures can help organizations prevent unauthorized access to personal data, safeguarding the privacy and security of sensitive information. Failure to implement appropriate encryption measures can result in significant fines and penalties under the GDPR, emphasizing the importance of encryption in maintaining compliance and trust in the digital world.
2 HIPAA
The HIPAA (Health Insurance Portability and Accountability Act) is a U.S. federal law enacted in 1996 to protect the privacy and security of individuals’ health information. It sets standards and regulations for healthcare providers and other related entities to ensure the confidentiality, integrity and availability of information. Although HIPAA does not explicitly mandate encryption, it requires covered entities to implement appropriate safeguards to secure patients’ electronic protected health information (ePHI) when the data is at rest, stored on a server, desktop file, USB drive, etc. HIPAA considers encryption an “addressable” specification. This means that organizations must assess whether it’s a reasonable and appropriate safeguard for their environment. If they determine that encryption is necessary, they must implement it. However, if they decide encryption is neither reasonable nor appropriate, they must document their reasoning and implement an equivalent alternative measure to protect ePHI.
3 NIS2 Directive
The NIS2 Directive (Network and Information Systems Directive) is a European Union legislative framework to improve the overall security and resilience of network and information systems. In the NIS2 Directive context, encryption plays a vital role as it is a crucial security measure to safeguard critical infrastructure, sensitive data and digital services. NIS2 explicitly requires encryption only for providers of public electronic communications networks or publicly available electronic communications services. Although not expressly mandated for other sectors, encryption technologies might be crucial to a comprehensive security strategy for digital infrastructure operators and domain specialists aiming to adhere to the NIS2 Directive. This encompasses maintaining the confidentiality, integrity and accessibility of data. By implementing end-to-end encryption, organizations can comply with the NIS2 Directive’s requirements, enhance their cybersecurity posture and contribute to a more secure and resilient digital ecosystem within the European Union.
4 CCPA
The CCPA (California Consumer Privacy Act) is a critical piece of legislation that aims to enhance privacy rights and consumer protection for residents of California. Enacted in 2018, the CCPA sets strict guidelines for businesses with regard to collecting, processing and storing the personal information of Californian consumers. The CCPA does not explicitly mandate encryption but highly encourages its implementation as a security measure. While encryption may not be a requirement, penalties are imposed on companies experiencing data breaches involving “non-encrypted or non-redacted personal information,” with fines reaching up to $750 per consumer per incident or actual damages. Organizations can potentially avoid these fines and protect their data by employing encryption solutions.
5 GeschGehG
The GeschGehG (German Law on the Protection of Trade Secrets) protects business secrets against unauthorized acquisition, use and disclosure. The law requires that secret information be protected by “appropriate secrecy measures” to ensure it remains confidential. With encryption solutions, businesses can protect their sensitive data (such as business plans, advertising strategies, customer lists, construction plans, recipes, prototypes and processes) from unauthorized access. This, in turn, helps companies comply with the GeschGehG and safeguard their trade secrets.
Staying vigilant and proactive in a dynamic digital world
In today’s rapidly evolving digital landscape, the looming threat of data breaches and the potential loss of sensitive information is a constant concern. IT experts must stay one step ahead of cyber threats and ensure that the trust of our users remains unshaken. By embracing compliance, staying informed and harnessing the power of encryption, we can successfully navigate the challenges of this ever-changing digital world and ensure the security of our data and communications.